Richi Jennings asks if it’s too soon to force Passkeys? I say as long as the user has devices that support Passkeys then no, it’s not too soon to push users in that direction as long as you keep alternatives around for their older devices… for now.
In just this one week, I was prompted by CVS.com and eBay to set a PassKey. I then went to GitHub and enabled PassKeys on both my GitHub accounts. The future is password-less! #KillThePassword
1Password is still offering to cover your costs in switching from a competitor to 1Password. Why am I reminding you of this? Reading the latest from LastPass makes me angry. (referral link to 1Password)
Zero Trust principles are built to support working from assumed-compromised environments. twitter.com/weldpond/…
A long time coming but I finally wrote some words about the SSO Tax
Another Password Manager Leak Bug: But KeePass Denies CVE - Security Boulevard:
Two researchers report vulnerability in KeePass. But lead developer Dominik Reichl says it’s not a problem—and refuses to fix the flaw. The issue is that KeePass has this weird feature that queues up a cleartext password export for the next time you authenticate. And that feature is itself configured via a plain-text config file, writable in the user’s security context. This strikes many as dangerous. However, Reichl blames the victim, saying an exploit would be the notional user’s fault for using an insecure device.
I have been a 1Password user since… well, I don’t remember. I do remember waiting eagerly for 1Password to launch on the iPhone - I have 1Password and 1Password Pro in my early purchase history.
I’ve been happy with them ever since. No major security vulnerabilities, responsive and quick to answer/clarify technical questions on how they’re keeping our data safe and not once have I seen a “you’re holding it wrong” response or any other type of victim blaming.
Many years ago at my previous employer, we wanted to make 1Password available to all our employees, recognizing that although our path was passwordless, security began at home. One phone call later, we were offered 1Password for both Mac and Windows for 5 devices for every license we purchased. This was back in the days of perpetual licensing - was this the genesis of 1Password for Business including 1Password for Families?
I also had an early briefing on the 1Password cloud service when they were only supporting Dropbox and iCloud, and how they were determined to truly minimize how much information they knew about their users and never having access to the contents of the vaults.
In the years since then, I’ve heard many complaints about their pricing model changing - while I can’t put a price on keeping my passwords and other secrets safe, 1Password is a no brainer for me. When we started Procella we instantly switched from individual 1Password for Families to 1Password for Business. which includes protection for up to 5 family members.
We’ve setup referrals for 1Password, but if you have 10 or more seats, talk to us first :)
1Password defined the password management business. Other companies have come and gone but 1Password still defines it for me. Unless you’re on BitWarden, it’s time to switch.
Lastpass and GoTo's continuing story
The GoTo attack has already had a major impact. In December, GoTo's LastPass secure password management division announced that the incident resulted in a subsequent hack of its cloud infrastructure and the theft of backups containing basic customer account information and - more importantly - customer vault data from the encrypted storage container including (fully-encrypted) fields such as website usernames and passwords, secure notes, and form-filled data. The company said it engaged the security firm Mandiant to investigate the incident and that the subsequent investigation revealed that attackers detected "unusual activity within our development environment and third-party cloud storage service," which is shared by both GoTo and its affiliate, LastPass.
If one area of your business was breached - how sure are you that it would be contained to that area and not spread out to the rest of your environment (including dev and prod)? Would you even notice the lateral spread of an attacker? Deploying a microsegmentation solution is a critical piece of a Zero Trust strategy. A good microsegmentation deployment will give you both visibilty and control to limit the spread - even if you haven’t deployed in a full segmentation mode. Continuous authentication including robust MFA and Zero Trust access are other key pieces which can also help limit your exposure.
Key lesson - assume you will be breached (or you already are!) - how are you limiting the damage from that breach?
If I think about it I shouldn’t be surprised this is possible but it still creeps me out. I was unhappy with a proposal to put occupancy sensors at desks but this is a whole new level.
Inspector General: 21% of DOI Passwords Easily Compromised in Test
In all, the OIG was able to crack 21% of the DOI passwords, and 16% of those were cracked within the first 90 minutes of testing. There were 14 agencies tested, including the Bureau of Indian Affairs (BIA); the Bureau of Land Management (BLM); the Bureau of Reclamation (BOR); the Bureau of Trust Funds Administration (BTFA); the Interior Business Center (IBC); the Minerals Management Service (MMS); the Bureau of Ocean Energy Management (BOEM); the Bureau of Safety and Environmental Enforcement (BSEE); the Office of Natural Resources Revenue (ONRR); the National Park Service (NPS); the Office of Inspector General (OIG); the Office of Surface Mining Reclamation and Enforcement (OSMRE); the U.S. Fish and Wildlife Service (FWS); and the U.S. Geological Survey (USGS).
Users cannot generate safe passwords. Organizations need to accept this and mitigate.
- Block easily cracked passwords at the reset page (even just running through the Have I Been Pwnd API would help.
- Enable and enforce MFA.
- Develop a plan to get to a passwordless environment.
1Password is making it as easy as possible to switch from a competitor
1Including crediting the remainder of your invoice to a competitor.
- affiliate link [return]
Internet Crime Complaint Center (IC3) | Cyber Criminals Impersonating Brands Using Search Engine Advertisement Services to Defraud Users
Use an ad blocking extension when performing internet searches. Most internet browsers allow a user to add extensions, including extensions that block advertisements. These ad blockers can be turned on and off within a browser to permit advertisements on certain websites while blocking advertisements on others.
So many good choices out there. Make sure you’re using one that utilizes the browser native content blocking functionality both for performance and privacy.
Re-reading about the 1Password secret key and feeling good about being all in on 1Password :)
A new(ish) start
I posted before about starting Procella. However, even as we started talking to prospective customers, Akamai was still my part time job… providing a safety net, great opportunities, but also an excuse to not push Procella to where it should be.
After just a month shy of 22 years, that is no longer the case. Today is my last day at my comfortable place. Akamai has been great to my career and my personal life. Too many friends to count. Too many opportunities given and taken to list. This day has been coming for the last 3 years but I’m still processing it.
Thank you to everyone, past and current at Akamai for supporting me. Thank you to all the vendors and customers for the challenges that we overcame. And the biggest thank you of all to my wonderful, amazing, supportive wife Melissa.
If you need a security assessment, Zero Trust roadmap assistance or anything related - find me at Procella!
A great read but what isn’t being said enough is that you can use Akamai MFA today with any site that supports FIDO2. No need to carry hardware tokens for Twitter, GitHub, etc - use your phone and upgrade your authentication game.
Segment, authenticate, authorize. Akamai, IoT and Zero Trust
Announcing Procella Technologies
In 2019 after 19 years at Akamai, mostly in IT, I decided it was time for a change.
There is of course, a longer version of this, but in late 2016 we had realized that the journey we had been taking Akamai IT on was actually a Zero Trust journey. Working closely with the Enterprise product team to make this journey a reality for Akamai customers over the last couple of years has been a joy and privilege.
I approached my manager and friend Joe DeFelice (Akamai’s IT CISO) with the idea to double down on the Zero Trust focus - sharing our experience and knowledge in this space with many more enterprises ranging from those who have heard of Zero Trust through those who may have started on their journey but are running into roadblocks.
We spoke about this idea with leaders in Akamai, the overwhelming response was positive and very supportive. Joe and I agreed to stay through March 2020 in order to continue supporting the Zero Trust transformation in IT, product development, and ecosystem expansion.
March 2020. The March that never ended. Fortunately, there was still enough work for Joe and I at Akamai to stay fully engaged. While our dream of doing our part to drive Zero Trust adoption broadly remained alive, it didn’t feel like the right time to be trying to start a new company when everyone was focused on learning how to be productive remotely. We were lucky enough to be able to stay on at Akamai during the pandemic, talking to customers, working with product managers and engineers and staying connected to IT. One thing above all else that I took away from 2020 - the more Akamai customers we spoke to, the more energized about helping companies with Zero Trust I became.
So it is with great pleasure I am writing this long post to introduce the company I am starting with Joe: Procella Technologies. Procella’s focus is Zero Trust and SASE. Our goal is to increase adoption of Zero Trust principals, and ensure enterprises are able to complete their Zero Trust or SASE journeys. If you’re considering Zero Trust or SASE, contact us to see how we can help.
The best path to password elimination is through federated authentication. The SSO tax is currently too high. Not just in penny pinching upgrades but in the obstacles to successfully enabling it.
I just tested a security integration with Microsoft 365 that was seriously just a couple of clicks. Then I tried to enable SAML which was a lot of copy and paste and changing fields. High potential for human error. We MUST do better here.
Thanks Dr Zerotrust. We don’t say it often enough - Akamai’s #zerotrust solutions were evolved working closely with customers implementing them including Akamai’s IT team. Proven in the real world.
So many things wrong here. An “emergency communications channel” protected by a widely shared username and password? Unauthorized use perhaps, but not hacking. And if you do have shared credentials, not rotating them after a high profile firing is insane. #zerotrust #authenticateallthethings
A reminder that cloud service providers hold a lot of control over your systems and data. Contracts and SLAs can’t protect you. If they pull the plug you’re the one picking up the pieces. Choose carefully.
IT teams: if you’re struggling to support a flood of WFH - don’t compromise on security or performance. Akamai’s EAA adds CDN performance and protection to your enterprise applications and scales well. This is how we are eliminating our own VPN usage at Akamai. #zerotrust #novpn #killthepassword
This mirrors my thoughts exactly. Why would you trust a VPN provider (and their providers) more than your own provider? Outsourcing privacy seems like a pretty big failure point. Make sure all your traffic is encrypted, push for eSNI and ditch the 3rd parties?
This is a pretty good read on “why zerotrust?” securityintelligence.com/posts/why… #zerotrust
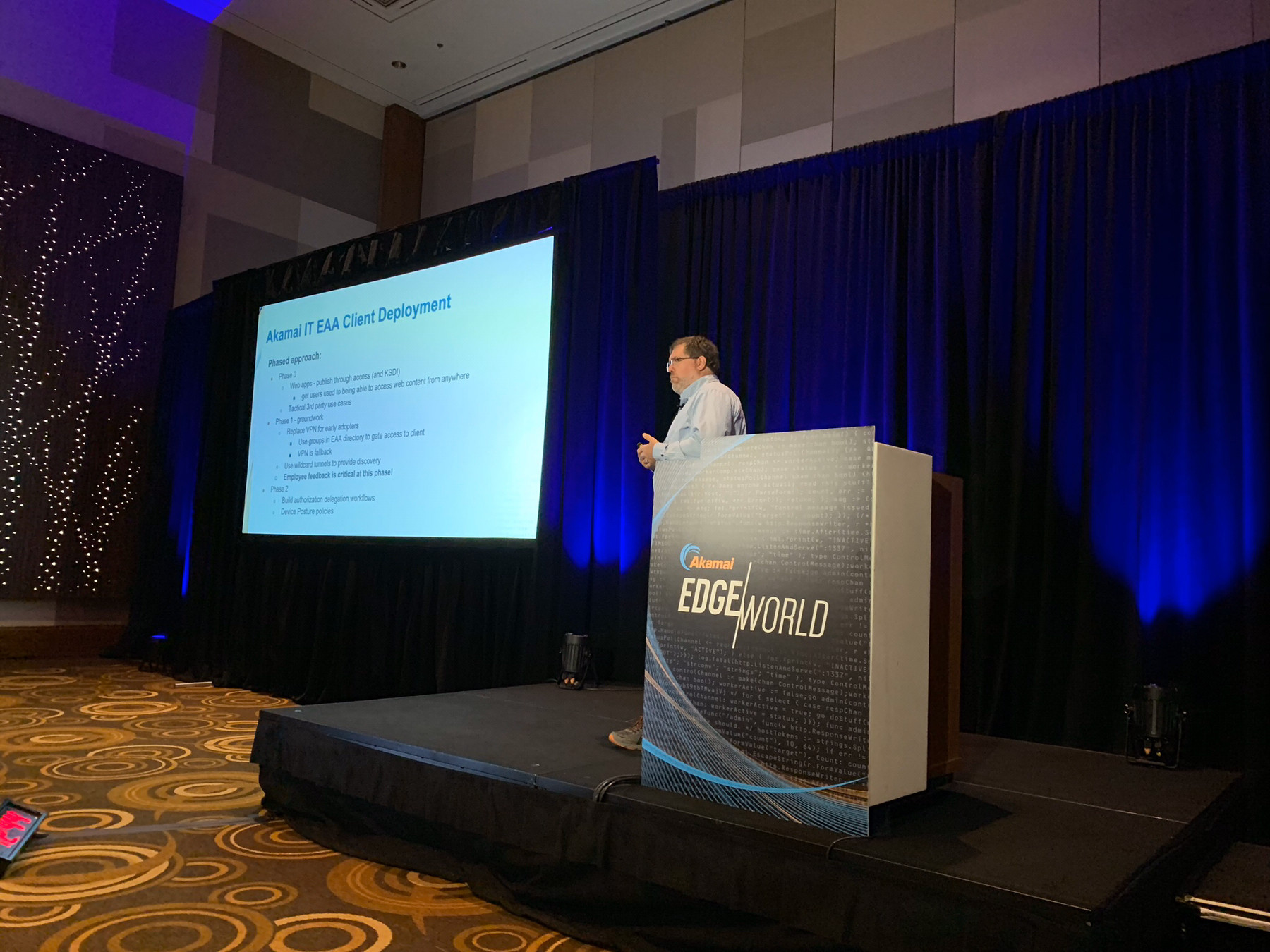 sharing my insights on how to move an enterprise to a zerotrust access model. #mbfeb
sharing my insights on how to move an enterprise to a zerotrust access model. #mbfeb