“This Is Not The Computer For You” · Sam Henri Gold
“This Is Not The Computer For You” · Sam Henri Gold:
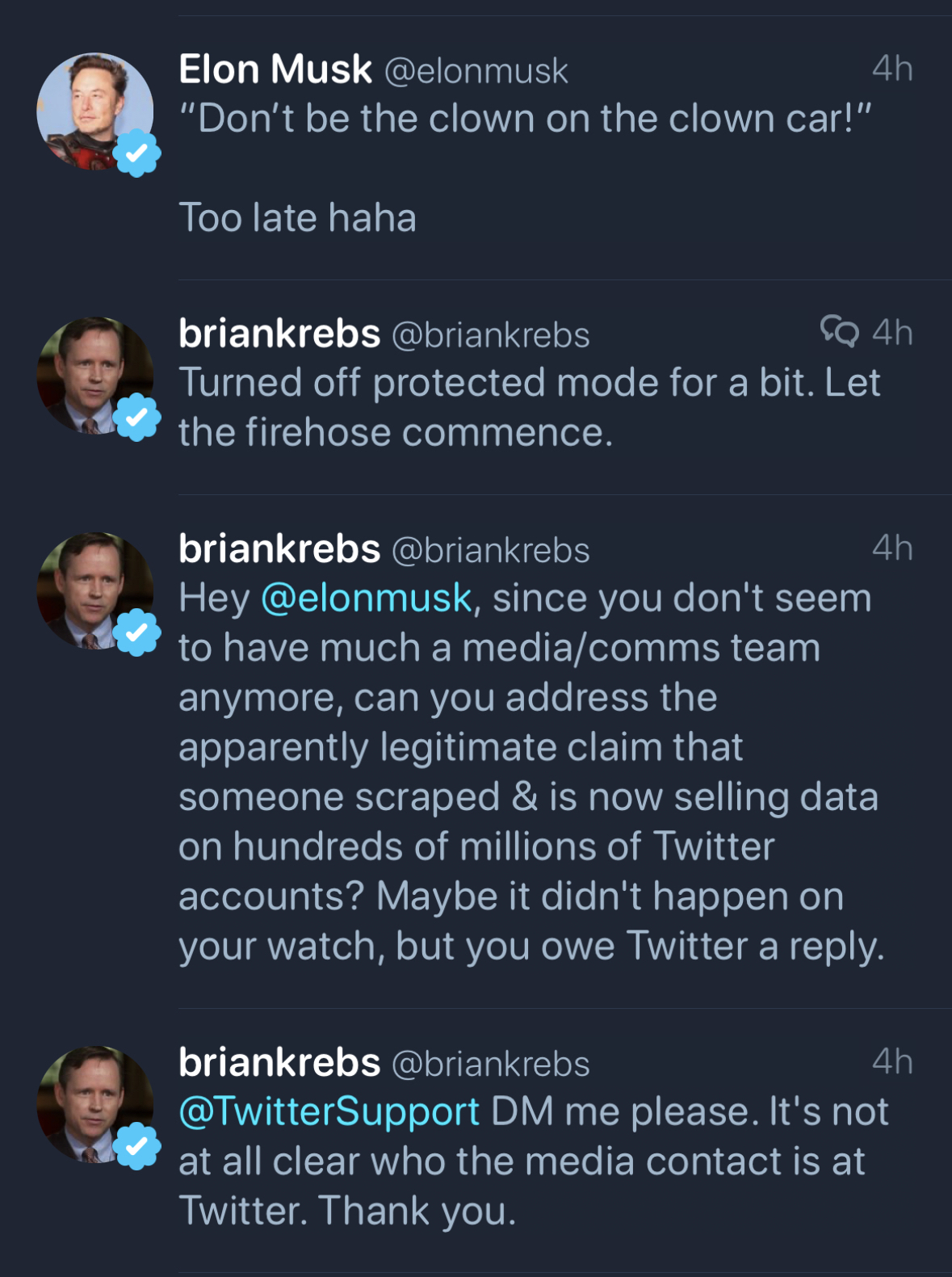
Yes, you will hit the limits of this machine. 8GB of RAM and a phone chip will see to that. But the limits you hit on the Neo are resource limits — memory is finite, silicon has a clock speed, processes cost something. You are learning physics. A Chromebook doesn’t teach you that. A Chromebook’s ceiling is made of web browser, and the things you run into are not the edges of computing but the edges of a product category designed to save you from yourself. The kid who tries to run Blender on a Chromebook doesn’t learn that his machine can’t handle it. He learns that Google decided he’s not allowed to. Those are completely different lessons.
It is wonderful that computing is ever more accessible to school kids. Chromebooks are now everywhere, phones are more computationally powerful than the supercomputers of my youth, and would absolutely smoke the 486 PC I built in college. But these are locked down environments. Learning by testing the limits is testing the limits of what you’re allowed to do, not what the device is capable of.
My memories include:
- Getting an Acorn Electron for Christmas because it was closest to the BBC Micro that my primary school had, and this made it an educational tool not a toy like my friends’ Spectrums.
- Spending multiple nights with my dad transcribing games written in BASIC from Electron User magazine to spend maybe an hour playing it before moving to the next. But always going back and trying to “improve” those games.
- Learning the basics of 6502 assembly language because that would unlock new areas to explore.
- Playing with the Doomsday Book on laserdisc on my primary school’s most advanced computer - a BBC Master.
- As soon as the teacher was occupied figuring out how to do literally anything else on it without getting busted.
- Gaining lunch time and out of hours access to my high school’s business studies computer room to work on the school newspaper and event programs.
- Learning how to safely disconnect one of the 80186 (yes!) computers from the 10base2 network without crashing the whole network, rebooting it out of the network-locked OS to play random PC games.
- Learning how to connect one of those PCs to the main school network which had much cooler software (there was a cable in the room to allow weekly backups of the business studies server).
- Discovering what was possible with the admin password we, uhh, obtained.
- Being recruited by the computer science department to help run the entire school network (so many fun stories there)
- Getting work experience at a local IBM sales office
- Learning about OS/2 and mainframes
- Figuring out how to download satellite images (through FTP by email) of Hurricane Andrew and stitch them together to make a slow, small, stuttering movie
- Getting employed by IBM and finally having Internet access (well, email anyway)
- Learning how IBM mail relays worked and how easy it was to spoof email as pranks
- Getting access to GOPHER servers at University
- Finding the hidden telnet services on specific GOPHER servers that gave me shell access
- Reading RFCs to understand how to send email via telnet, or read news via telnet or why FTP wouldn’t transfer files through telnet
- Realizing that early HTTP was not hugely dissimilar to GOPHER, and that we had a couple of mainframes at IBM with access to the internal IP network, and someone had already written a GOPHER server for the mainframe. Stretching that GOPHER server into HTTP and figuring out how to share my Office/VM calendar as a webpage.
- Spending all my money on building a PC and not having enough to buy a copy of Windows (or even DOS)
- Downloading 40 disk images of slackware via FTP by email and screen scraping the 3270 session at work
- Getting a real ISP at home (dial up of course)
- Sharing the house with 2 other nerds who also wanted Internet access especially after we ran Ethernet and Token Ring through the house to host LAN parties.
- Before NAT we had experience with SOCKS and HTTP proxies, so I wrote a SOCKS and HTTP Proxy that would initiate a dialup if it wasn’t already connected.
Where are the opportunities or incentives for my kids to do anything like this? They have chromebooks from school for school work. They have access to their parents macs if they need to do research for scouts or other extra curriculars, but realistically they have access to more computing power than I imagined when I was a kid and its just a way for them to watch videos, listen to music or podcasts or play games. They aren’t trying to break out of the limitations (other than screen time) because they have what they need - “it just works”. But does “it just work” end up stifling imagination of what could be possible beyond what’s allowed by the device? And why am I only thinking about this now with my eldest thinking about colleges?